add formulas to complete the table of hours used. in cell b17, create a nested formula with the IF and SUM functions that check if the total number of hours worked in week 1 (cells b9:f9) is equal to 0. If it is, the cell should display nothing (indicated with two quote marks: '' ''). Otherwise, the cell should display the total number of hours worked in week 1. Copy the formula from cell b17 to fill the range b18:b20.
Answers
To create a nested formula with the IF and SUM functions that checks if the total number of hours worked in week 1 is equal to 0 and displays the total number of hours worked if it is not 0, you can use the following formula in cell B17: =IF(SUM(B9:F9)=0, "", SUM(B9:F9))
What is a Nested Formula?Nested (or inner, nested) functions are applied written within other functions that allow us to immediately access the variables and names declared in the enclosing function. Nested functions may be used to create closures and decorators, among other things.
Simply copy the formula from cell B17 and paste it into cells B18:B20 to fill the range B18:B20 with the same formula.
Learn more about Nested Formulas;
https://brainly.com/question/27531742
#SPJ1
Related Questions
In cell G5, enter a formula without using a function that subtracts the actual dollars billed from the estimated amount to determine the remaining amount of the estimate for general administrative services
Answers
Using the appropriate excel syntax, the formula which calculates the actual amount from estimated amount is : =C10 - D10
Using the cells thus :
Actual dollar billed = C10Estimated amount = D10Using the cell values defined above ; the required excel syntax is as follows :
=C10 - D10Note : All excel formulas begin with the equal to sign.
Learn more : https://brainly.com/question/25644130
Which functions are examples of logical test arguments used in formulas? Check all that apply. OR IF SUM COUNT NOT AND
Answers
Answer: Which functions are examples of logical test arguments used in formulas? Check all that apply.
Explanation: A.or B.if E.not F. And
This is correct just took it :)
Among the following functions, those that are the logical test arguments used in formulas are OR, IF, NOT and, AND.
What are logical test argument functions ?To compare several conditions or numerous sets of conditions, logical functions are utilized. By weighing the arguments, it determines if the answer is TRUE or FALSE.
These operations are used to determine the outcome and aid in choosing one of the available data. The contents of the cell are assessed using the appropriate logical condition depending on the necessity. The types of logical functions used in this tutorial include: OR, AND, IF, NOT and XOR.
These all functions are used in different conditions. Therefore, for the given options the logical testing arguments are OR, IF, NOT and, AND. They are very common functions in Excel sheet.
Find more on logical functions :
https://brainly.com/question/27053886
#SPJ3
Define a function isset that tests whether a bag is actually a set, which is the case when each element occurs only once. isSet : Bag a -> Bool
Answers
The isset() method determines if a variable has been set, which indicates it has been defined and is not NULL. If the variable exists and is not NULL, this method returns true; otherwise, it returns false.
What syntax does the isset () function provide?The isset() function is a built-in PHP function that verifies whether a variable is set and not NULL. This method also tests to see if a defined variable, array, or array key contains a null value; if it does, isset() returns false; otherwise, it returns true. bool isset($var, mixed) syntax In PHP, use the isset() function to determine whether or not the form was properly submitted. Use the isset() function in the code to verify the $_POST['submit'] method. Remember to define the name of the submit button in lieu of submit. After hitting the submit button, this action will be performed via the POST method.
Learn more about array key from here;
https://brainly.com/question/28900889
#SPJ4
9. In a 208-volt Y-connected system, what is the voltage drop between any phase wire and the grounded
neutral center tap of the windings?
A. 262 VAC
B. 180 VAC
C. 120 VAC
D. 240 VAC
Answers
A victimless crime is committed when
|. Select 3 options.
someone downloads a pirated song or video
a copyrighted image is used without permission
a stranger accesses your internet banking
a person downloads and uses pirated software
a hacker sells a company's financial statements
Answers
A victimless crime is committed when a copyrighted image is used without permission 2. a stranger accesses your internet banking 3. a hacker sells a company’s financial statements.
Victimless crimes are illegal acts that break the laws, but there is no single victim of the crime. They are against social values and laws. A copyrighted image is used without permission
Examples are gambling, traffic violations, etc. Thus, Victimless crimes differ from other types of crime because it does not have an identifiable victim. This crime is against laws and social values and beliefs.
To know more about victimless crimes, visit:
brainly.com/question/17251009
#SPJ6
alle Mbawah: Attempt 1 How does a bystander become an advocate? By harassing the bully until he or she stops the harmful activity By taking action in either reporting the bully or otherwise supporting the victim By ignoring the situation By becoming a victim him- or herself to show concern Question 3 (5 points) alle Mbawah : Attempt 1 How does a bystander become an advocate ? By harassing the bully until he or she stops the harmful activity By taking action in either reporting the bully or otherwise supporting the victim By ignoring the situation By becoming a victim him- or herself to show concern Question 3 ( 5 points )what is the ans
Answers
Answer:By reporting the bully or supporting the victim that's what I would do
Explanation:
A bystander becomes an advocate by taking action in either reporting the bully or otherwise supporting the victim. Thus, the correct option for this question is B.
What is an Advocate?An advocate may be characterized as a type of person that supports another person in order to help you express your views and wishes, and help you stand up for your rights. It is the one who pleads with another's cause, who helps another by defending or comforting him.
According to the context of the story, a bystander has their own responsibilities in case of any harmful activities going out in their surroundings. They are required to take action in either reporting the bully or otherwise supporting the victim. In this case, harmful activities reduce from our surroundings. Everything required some actions and initiations.
Therefore, the correct option for this question is B.
To learn more about Advocate, refer to the link:
https://brainly.com/question/26054678
#SPJ2
2. Which is not part of the Sans Institutes Audit process?
Help to translate the business needs into technical or operational needs.
O Deler a report.
O Define the audit scope and limitations.
O Feedback based on the
Answers
Answer:
Help to translate the business needs into technical or operational needs. This is not a part.
Explanation:
Capital budgeting simply refers to the process that is used by a business in order to determine the fixed asset purchases that is proposed which it should accept, or not. It's typically done in order to select the investment that's most profitable for a company.
Some of the capital budgeting processes include:
Identification and analysis of potential capital investments.
Application of capital rationing
Performing post-audits
It should be noted that developing short-term operating strategies is not part of the capital budgeting process.
Learn more about investments on:
https://brainly.com/question/15105766
#SPJ2
magine that you are designing an application where you need to perform the operations Insert, DeleteMaximum, and Delete Minimum. For this application, the cost of inserting is not important, because itcan be done off-line prior to startup of the time-critical section, but the performance of the two deletionoperations are critical. Repeated deletions of either kind must work as fast as possible. Suggest a datastructure that can support this application, and justify your suggestion. What is the time complexity foreach of the three key operations
Answers
Answer:
Use the stack data structure with both best-case and worst-case time complexity of O(1) for insertion and deletion of elements.
Explanation:
The stack data structure is used in programs to hold data for which the last data in the stack is always popped out first when retrieving the data sequentially, that it, first-in, last-out.
The elements in the stack are located in an index location, which means that they can be retrieved directly by choice with constant time complexity of 1 or O(1) for best and worst-case.
So inserting, and deleting the minimum and maximum elements in the stack data structure executes at a speed of the constant 1 (big-O notation, O(1) ).
What is one still image in a film or video called?
unit
frame
stand
selection
Answers
Answer:
frame
Explanation:
the answer is frame ;)
Answer:
Frame
A still frame is a single static image taken from a film or video, which are kinetic (moving) images. Still frames are also called freeze frame, video prompt, preview or misleadingly thumbnail, keyframe, poster frame, or screen shot/grab/capture/dump
Explanation:
Pls mark as brainliest
Describe three things (risks) that can cause damage to computer hardware
Answers
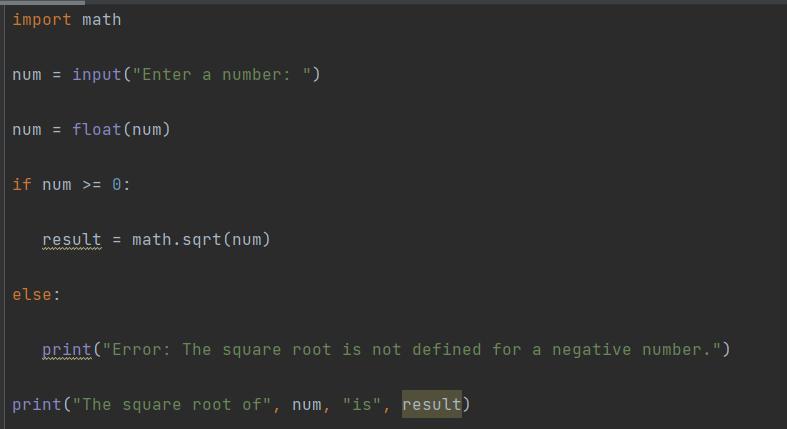
write a python program as jupyter notebook to accomplish the following tasks note: use input statement and if statement. in addition, use import math.
Answers
A Python program that gives the square root of a positive number achieves the desired tasks, and is given as follows:
import math
num = input("Enter a number: ")
num = float(num)
if num >= 0:
result = math.sqrt(num)
else:
print("Error: The square root is not defined for a negative number.")
print("The square root of", num, "is", result)
How to define the program?The first step is importing the math library, with the following command:
import math.
Then the number, which can be decimal, is read from the user, as follows:
num = input("Enter a number: ")
num = float(num)
Then the conditional statement is used to verify if the number possesses a square root of not, that is, if the number is not negative, as follows:
if num >= 0:
result = math.sqrt(num)
else:
print("Error: The square root is not defined for a negative number.")
Finally, the square root is printed, as follows:
print("The square root of", num, "is", result)
More can be learned about Python Programming at https://brainly.com/question/26497128
#SPJ1
1. State three types of web protocols
Answers
Answer:
Types of Protocols
Transmission Control Protocol (TCP)
Internet Protocol (IP)
User Datagram Protocol (UDP)
Post office Protocol (POP)
Simple mail transport Protocol (SMTP)
File Transfer Protocol (FTP)
Hyper Text Transfer Protocol (HTTP)
Hyper Text Transfer Protocol Secure (HTTPS)
Drag each label to the correct location on the image. Match each mode dial icon with its appropriate icon.allows you to choose and control the shutter speedis ideal for taking close-up shots while holding the camera very close to the subjectproduces greater saturation and vivid colors and contrastis ideal for capturing moving subjectsgives the photographer full control of all settings
Answers
lets you select and manage the shutter speed. In this mode, the shutter speed can be entirely customised to the user's preferences, and the aperture is automatically adjusted.
What does a camera's Shutter Priority mode do?When a photographer manually selects a shutter speed for an exposure, the camera automatically selects an appropriate aperture and ISO setting to go with that shutter speed. This is known as shutter speed priority or shutter priority mode.
What three camera modes are there?Three types of shooting modes are available: scene, auto, P, S, A, and M modes. Shutter speed and aperture are managed by the camera in auto and scene settings. The exposure modes, or P, S, A, and M, provide photographers with a variety of options.
To know more about shutter speed visit:-
https://brainly.com/question/25000037
#SPJ4
In the article, “Protecting American Soldiers: The
Development, Testing, and Fielding of the Enhanced Combat Helmet”, Describe the features, functions and high-level tasks that were identified in the case study project deemed to be successful.
Answers
The features are: The primary goal of ballistic protection is to guarantee that the helmet can efficiently shield the head against hazardous ballistic hazards, including shrapnel and bullets, during times of combat to mitigate the probability of head injuries.
What is the article about?Other Characteristics:
Creating a helmet with robust impact resistance to mitigate the risk of head injuries resulting from falls, collisions, or explosions by minimizing skull fractures and brain damage.
The objective of the Lightweight Design is to achieve a harmonious equilibrium between safeguard and weight. This reduces discomfort and exhaustion for the wearer, allowing the soldiers to execute their tasks with efficiency, without being hampered by bulky headgear.
Learn more about Protecting American from
https://brainly.com/question/30707919
#SPJ1
What is the word to tell excel that you want it to do math
Answers
Are you referring to functions? In a cell you can type "=" and it will allow you to enter a formula to insert math equations involving other cell values.
Create an ArrayList of Countries
- Create a class called Country.java.
- Instance variables include name (String), capital (String), and population (an int representing the population of the capital)
- Write a 3-arg constructor
- Write 3 accessor methods
- Write a toString method that returns the state/value of all instance variables.
- Test out your class:
- Step 1: Create an ArrayList of five countries.
- Step 2: Print out your ArrayList.
- Step 3: Remove one of the countries.
- Step 4: Print out your ArrayList again.
- Step 5: Create a new country and insert it in the middle of your ArrayList.
- Step 7: Print out your ArrayList again.
- Step 8: Change your last country to the country you removed in Step 3.
- Step 9: Print out your ArrayList again.
Answers
Answer:
Step 1: Create an ArrayList of five countries by creating Country objects and adding them to the ArrayList.
Step 2: Print out your ArrayList by looping through it and printing out each Country object's toString() method.
Step 3: Remove one of the countries from the ArrayList by using the remove() method and passing in the index of the object you wish to remove.
Step 4: Print out your ArrayList again by looping through it and printing out each Country object's toString() method.
Step 5: Create a new country and insert it in the middle of your ArrayList by creating a Country object and using the add() method with the index of the position in the ArrayList.
Step 6: Print out your ArrayList again by looping through it and printing out each Country object's toString() method.
Step 7: Change your last country to the country you removed in Step 3 by first removing the last country from the ArrayList, creating a new Country object using the same parameters as the one you removed earlier, then using the add() method with the index of the last position in the ArrayList.
Step 8: Print out your ArrayList again by looping through it and printing out each Country object's toString() method.
What should you do when you are working on an unclassified system and receive a classified attachment?
Answers
If a classified attachment is sent to you while you are working on an unclassified system, call your security point of contact immediately.
What is the meaning of classified documents?
Material that a government agency deems to be sensitive information that needs to be protected is classified information. Laws and regulations limit access to specific groups of people with the required security clearance and need to know, and improper handling of the information can result in criminal penalties.
What is the meaning of unclassified information?
Official information that does not require the assignment of Confidential, Secret, or Top Secret markings but is not publicly-releasable without permission is classified as unclassified.
To know more about unclassified information, check out:
https://brainly.com/question/28302335
#SPJ1
Discuss in details the difference among programmed I/O, Interrupt Driven I/O
and Direct Memory access over the processor
Answers
Answer:
Programmed I/O, Interrupt Driven I/O, and Direct Memory Access (DMA) are three methods of transferring data between input/output (I/O) devices and the central processing unit (CPU) of a computer system.
Programmed I/O:
In programmed I/O, the CPU executes instructions to transfer data between the I/O device and memory. The CPU continuously polls the I/O device to check if it is ready to send or receive data. This method is simple and easy to implement, but it is also inefficient since the CPU has to wait for the I/O device to be ready before it can perform any other task.
Interrupt Driven I/O:
In interrupt-driven I/O, the CPU sends a command to the I/O device to start the data transfer, and then continues to perform other tasks. When the I/O device has completed the data transfer, it interrupts the CPU to signal that the data is ready. The CPU then stops its current task and processes the interrupt by executing an interrupt service routine (ISR) to transfer the data between the I/O device and memory. This method is more efficient than programmed I/O since the CPU can perform other tasks while waiting for the I/O device to complete the data transfer.
Direct Memory Access (DMA):
In Direct Memory Access (DMA), the I/O device can access the system memory directly without the intervention of the CPU. The I/O device sends a request to the DMA controller to initiate the data transfer, and the DMA controller transfers the data between the I/O device and memory without any involvement of the CPU. The CPU can continue to perform other tasks while the DMA controller performs the data transfer. This method is the most efficient of the three since it frees up the CPU to perform other tasks while the data transfer is being performed.
In summary, the main differences among programmed I/O, interrupt-driven I/O, and DMA are:
Programmed I/O is the simplest method of data transfer, but it is also the least efficient since the CPU has to continuously poll the I/O device to transfer data.
Interrupt-driven I/O is more efficient than programmed I/O since the CPU can perform other tasks while waiting for the I/O device to complete the data transfer.
DMA is the most efficient method of data transfer since it frees up the CPU to perform other tasks while the DMA controller performs the data transfer directly between the I/O device and memory.
Write a program to find a peak in an array of ints. Suppose the array is {-1, 0, 2, 5, 6, 8, 7}. The output should be "A peak is at array index 5 and the value is 8." This is because the value 8 is larger than its predecessor 6 and its successor 7 in the given array. Note that 8 occurs at index 5. (The array starts at index 0.) A number at index i in an array X is considered a peak if: X[i]>=X[i-1] and X[i]>=X[i+1]. If i is at the beginning of the array, then peak is if X[i]>=X[i+1]. If i is at end of array, then peak is if X[i]>=X[i-1].
Answers
Answer:
Following are the code to this question:
#include<iostream>//declaring header file
using namespace std;
int main()//main method
{
int n= 6,j=0;//declaring integer variable
int X[n];//defining an array
for(j=0;j<=n;j++)//defining a loop for input value
cin>>X[j];//input value from the user
if(j==0) //defining if block that checks value at beginning
{
if(X[j]>=X[j+1])//defining if block to check to compare first and second value
{
cout<<"A peak is at array index "<<j<<" and the value is "<<X[j];//use print method to largest value with index number
}
}
else//defining else block
{
for(j=0;j<=n;j++)//defining for loop for compare other value
{
if(j==n-1) //use if block that checks next index
{
if(X[j]>=X[j-1])//use if block to compare value
cout<<"A peak is at array index "<<j<<" and the value is "<<X[j];//use print method to largest value with index number
}
else
{
if(X[j]>=X[j-1] && X[j]>=X[j+1])//comapre value
cout<<"A peak is at array index "<<j<<" and the value is "<<X[j];//use print method to largest value with index number
}
}
}
return 0;
}
Output:
please find the attached file.
Explanation:
In the given code, inside the main method two integer variable "n and j", is declared, in the next step, an array "x"is defined which input the value from the user end.
In the next step, multiple if block is used, in the first if block it comapre the first and second value if it grater then it will print the value with its index number.In the next if block, it comapre is next value and if it grater then it will print the value with its index number.
which network type Is used in office or building?
Answers
Answer:Local Area Network (LAN) is typically used in offices or buildings.
Explanation:
which network type Is used in office or building?
Answer:
LAN(local area Network
Explanation:
LAN(Local Area Network)
Local Area Network is a group of computers connected to each other in a small area such as building, office. LAN is used for connecting two or more personal computers through a
communication medium such as twisted pair, coaxial cable, etc.
i hope this helped
1. Add the following method to the Point class:
public double distance(Point other)
Returns the distance between the current Point object and the given other Point object. The distance between two points is equal to the square root of the sum of the squares of the differences of their x- and y-coordinates. In other words, the distance between two points (x1, y1) and (x2, y2) can be expressed as the square root of (x2 - x1)2 + (y2 - y1)2. Two points with the same (x, y) coordinates should return a distance of 0.0.
public class Point {
int x;
int y;
// your code goes here
}
2. Create a class called Name that represents a person's name. The class should have fields named firstName representing the person's first name, lastName representing their last name, and middleInitial representing their middle initial (a single character). Your class should contain only fields for now.
3. Add two new methods to the Name class:
public String getNormalOrder()
Returns the person's name in normal order, with the first name followed by the middle initial and last name. For example, if the first name is "John", the middle initial is 'Q', and the last name is "Public", this method returns "John Q. Public".
public String getReverseOrder()
Returns the person's name in reverse order, with the last name preceding the first name and middle initial. For example, if the first name is "John", the middle initial is 'Q', and the last name is "Public", this method returns "Public, John Q.".
4. Add the following method to the Point class:
public int quadrant()
Returns which quadrant of the x/y plane this Point object falls in. Quadrant 1 contains all points whose x and y values are both positive. Quadrant 2 contains all points with negative x but positive y. Quadrant 3 contains all points with negative x and y values. Quadrant 4 contains all points with positive x but negative y. If the point lies directly on the x and/or y axis, return 0.
public class Point {
private int x;
private int y;
// your code goes here
}
Answers
Answer:
Explanation:
The following code is written in Java and creates all of the methods that were requested in the question. There is no main method in any of these classes so they will have to be called from the main method and call one of the objects created method for the code to be tested. (I have tested it and it is working perfectly.)
class Point {
private int x, y;
public void Point(int x, int y) {
this.x = x;
this.y = y;
}
public double distance (Point other) {
double distance = Math.sqrt(Math.pow((other.x - this.x), 2) + Math.pow((other.y - this.y), 2));
return distance;
}
public int quadrant() {
if (this.x > 0 && this.y > 0) {
return 1;
} else if (this.x < 0 && this.y > 0) {
return 2;
} else if (this.x < 0 && this.y < 0) {
return 3;
} else if (this.x > 0 && this.y < 0) {
return 4;
} else {
return 0;
}
}
}
class Name {
String firstName, lastName;
char middleInitial;
public String getNormalOrder() {
String fullName = firstName + " " + middleInitial + " " + lastName;
return fullName;
}
public String getReverseOrder() {
String fullName = lastName + ", " + firstName + " " + middleInitial;
return fullName;
}
}
Does the security burden fall primarily on the user? On
the company that the user is doing business with? On
both? Support your answer.
Answers
Answer:
yes and no because of the security
Explanation:
yes and no because of the security
Pls due soon
Directions: Answer these questions as you navigate through the modules of the Computer Basics Tutorial.
Define computer:
What are the functions of a computer?
Name three ways in which you can use a computer?
Define hardware:
Define software:
Name at least four different types of computers.
What are the two main styles that personal computers come in?
What is the purpose of the operating system?
Name the three most common operating systems for PCs.
What does GUI stand for and what is its purpose?
In what year did Microsoft create Windows?
What is MAC OS?
What is Linux?
Name three operating systems designed specifically for mobile devices?
What is an App?
What are apps for mobile devices called?
Name six types of desktop applications?
Name three examples of mobile apps (does not have to come from the tutorial)?
What is the Cloud?
Name three services that use the Cloud?
Give at least one reason why someone would want to use the Cloud.
Give three examples of web apps?
What are the basic parts of a desktop computer and what purpose does each one serve?
Name two common mouse alternatives?
Name at least five peripherals?
What is the CPU/Processor of a computer?
How is the processor’s speed measured?
What is the motherboard and what purpose does it serve?
What does the power supply unit do?
What is RAM and what is it measured in?
What is a hard drive and what purpose does it serve?
What is the purpose of each of the following:
expansion card
video card
sound card
network card
Bluetooth card
What is a laptop computer and how is it different from a desktop computer?
What is a mobile device? Give three examples.
What is a smartphone?
What are 3G, 4G, and LTEs?
How is a tablet computer different from a laptop? What are some advantages and disadvantages of using a tablet?
What is the desktop and what features does it usually contain?
What is the purpose of using folders on the computer?
What is the purpose of the Recycle Bin?
Name three things you need to access the Internet?
Describe each of the following common types of Inter services:
Dial-up
DSL
Cable
Satellite
3G and 4G
What are some things you should consider when you are choosing and Internet Service Provider?
What is a modem?
What is a router?
What is a network card?
What does Wi-Fi stand for?
What is a web browser and what is its main job?
What is the World Wide Web?
Name three different types of web browsers?
Explain the following security terms:
SSID:
Encryption password
Encryption
Passphrase
What steps do you need to take to keep your computer healthy?
How do you deal with spilled liquid on your keyboard?
How do you clean the mouse and the monitor?
What is malware and what does it include? What is the best way to guard against malware?
In what ways can you back up your computer?
Name several techniques to maintain your computer?
Define computer ergonomics.
What are four general tips to keep in mind when troubleshooting your computer?
What is a flash drive?
What is Cloud storage?
What is the proper way to safely remove a flash drive from the computer?
Name three free popular services that allow you to save data to the Cloud?
What are accessibility features? Name three?
Name three assistive technology devices and what they are used for?
Answers
Answer:
Software for personal computers is typically developed and distributed independently from the hardware or operating system manufacturers. Many personal computer users no longer need to write their own programs to make any use of a personal computer, although end-user programming is still feasible. This contrasts with mobile systems, where software is often only available through a manufacturer-supported channel. And end-user program development may be discouraged by lack of support by the manufacturer.
Explanation:
Explain the social implication of computers on society in particular privacies and
quality of life.
Answers
The use of computers and technology has had a significant impact on society and the way people live their lives. One of the most significant social implications is the impact on privacy.
What is the computers about?The increased use of computers has led to the collection, storage, and sharing of vast amounts of personal information, including financial, medical, and personal data. This has raised concerns about the protection of personal privacy and the potential misuse of personal information by governments, corporations, and other entities.
Therefore, Another aspect of privacy that has been impacted by technology is online privacy. With the widespread use of the internet and social media, people are sharing more personal information online than ever before, leaving them vulnerable to online identity theft, hacking, and other forms of cybercrime.
Learn more about computers from
https://brainly.com/question/21474169
#SPJ1
Transmissions in wireless networks do not allow for collision detection but try to avoid collision. Briefly describe this process and explain why it is termed as unreliable.
Answers
Transmissions in wireless networks do not allow for collision detection but try to avoid collision and also It is especially crucial for wireless networks since wireless transmitters desensing (turning off) their receivers during packet transmission prevents the option of collision detection using CSMA/CD.
What are the different types of wireless transmission?Wireless transceivers are unable to send and receive on the same channel simultaneously, hence they are unable to identify collisions. This is because the send power (which is typically around 100mw) and the receive sensitivity have such a huge disparity (commonly around 0.01 to 0.0001mw).
Therefore, Infrared, broadcast radio, cellular radio, microwaves, as well as communications satellites are examples of wireless transmission media that are used in communications. Infrared (IR), which is a wireless transmission medium that uses infrared light waves to transmit signals, was covered previously in the chapter.
Learn more about collision detection from
https://brainly.com/question/14775265
#SPJ1
which statement is true for a career as a graphic designer?
Answers
Answer:
E. You need to generate and maintain digital content on various platforms.
Explanation:
N/A
Which sentence has correct parallel structure?
О А. The software allows users to create new documents, copying files from other sources, and saving new changes.
Users need a laptop, internet connection, and need an appropriate document editor.
SO B.
O C.
To install the application, connect the flash drive, run the setup, and restart the system.
OD.
The application bundle contains a DVD, the flash drive, and instruction manual.
Answers
The sentence that has parallel structure is "To install the application, connect the flash drive, run the setup, and restart the system." (opiton C)
What is parallel structure?The repeating of a certain grammatical form inside a phrase is known as parallel structure (also known as parallelism). A parallel construction is created by making each comparable object or notion in your phrase follow the same grammatical pattern.
Consider this example: "I forgave you when you lost my cat, when you left me at the airport, and when you threw out my favorite stuffed animal." The parallel structure is the recurrent usage of I forgave you when you.
Hence, option C is correct.
Learn more about parallel structure:
https://brainly.com/question/8055410
#SPJ1
Which of the following types of data can be stored using cloud computing? Check all of the boxes that apply.
photos
movies
documents
music
CORRECT: all 4 are correct
Answers
Note tht all the options can be stored using cloud computing. (A -- D)
what is Cloud Computing?
Cloud computing refers to the on-demand availability of computer system resources, particularly data storage and computational power, without the user's direct active supervision. Large clouds frequently have functions spread across numerous locations, each of which is a data center.
A wide range of services rely on cloud computing. This encompasses anything from consumer services like G. mail or the cloud backup of your smartphone's images to services that allow major organizations to host all of their data and operate all of their apps in the cloud.
Learn more about cloud computing at:
https://brainly.com/question/29737287
#SPJ1
Answer: All of them
Explanation:
Difference between Python vs Pandas?
Answers
Python and Pandas are not directly comparable as they serve different purposes. Here's an explanation of each:
Python:
Python is a general-purpose programming language known for its simplicity and readability. It provides a wide range of functionalities and can be used for various tasks, including web development, data analysis, machine learning, and more. Python has a large standard library and an active community, making it versatile and widely used in different domains.
Pandas:
Pandas, on the other hand, is a powerful open-source library built on top of Python. It is specifically designed for data manipulation and analysis. Pandas provides easy-to-use data structures, such as Series (one-dimensional labeled arrays) and DataFrame (two-dimensional labeled data tables), along with a variety of functions for data cleaning, transformation, filtering, grouping, and aggregation.
In essence, Python is the programming language itself, while Pandas is a Python library that extends its capabilities for data analysis and manipulation. You can use Python to write code for a wide range of purposes, while Pandas is focused on providing efficient and convenient tools for working with structured data.
for similar questions on Python.
https://brainly.com/question/26497128
#SPJ8
Which statement is true about computer security?
1.Computer security is the job of specialized security engineers.
2. Computer security is only necessary for governments and big businesses.
3.Computer security is everyone's responsibility.
4.Computer security does not affect the gaming industry.
Answers
Answer:
Computer security is everyone's responsibility.
Hope this helps! ^-^
-Isa