Part 1: For this assignment, call it assign0 Implement the following library and driver program under assign0: Your library will be consisting of myio.h and myio.c. The function prototypes as well as more explanations are listed in myio.h. Please download it and accordingly implement the exported functions in myio.c. Basically, you are asked to develop a simple I/O library which exports a few functions to simplify the reading of an integer, a double, and more importantly a string (whole line). In contrast to standard I/O functions that can read strings (e.g., scanf with "%s", fgets) into a given static size buffer, your function should read the given input line of characters terminated by a newline character into a dynamically allocated and resized buffer based on the length of the given input line. Also your functions should check for possible errors (e.g., not an integer, not a double, illigal input, no memory etc.) and appropriately handle them. Then write a driver program driver.c that can simply use the functions from myio library. Specifically, your driver program should get four command-line arguments: x y z output_filename. It then prompts/reads x many integers, y many doubles, and z many lines, and prints them into a file called output_filename.txt. Possible errors should be printed on stderr.
myio.h file
/*
* File: myio.h
* Version: 1.0
* -----------------------------------------------------
* This interface provides access to a basic library of
* functions that simplify the reading of input data.
*/
#ifndef _myio_h
#define _myio_h
/*
* Function: ReadInteger
* Usage: i = ReadInteger();
* ------------------------
* ReadInteger reads a line of text from standard input and scans
* it as an integer. The integer value is returned. If an
* integer cannot be scanned or if more characters follow the
* number, the user is given a chance to retry.
*/
int ReadInteger(void);
/*
* Function: ReadDouble
* Usage: x = ReadDouble();
* ---------------------
* ReadDouble reads a line of text from standard input and scans
* it as a double. If the number cannot be scanned or if extra
* characters follow after the number ends, the user is given
* a chance to reenter the value.
*/
double ReadDouble(void);
/*
* Function: ReadLine
* Usage: s = ReadLine();
* ---------------------
* ReadLine reads a line of text from standard input and returns
* the line as a string. The newline character that terminates
* the input is not stored as part of the string.
*/
char *ReadLine(void);
/*
* Function: ReadLine
* Usage: s = ReadLine(infile);
* ----------------------------
* ReadLineFile reads a line of text from the input file and
* returns the line as a string. The newline character
* that terminates the input is not stored as part of the
* string. The ReadLine function returns NULL if infile
* is at the end-of-file position. Actually, above ReadLine();
* can simply be implemented as return(ReadLineFile(stdin)); */
char *ReadLineFile(FILE *infile);
#endif
Answers
Answer:
Explanation:
PROGRAM
main.c
#include <fcntl.h>
#include <stdio.h>
#include <stdlib.h>
#include <sys/stat.h>
#include <sys/types.h>
#include <unistd.h>
#include "myio.h"
int checkInt(char *arg);
int main(int argc, char *argv[]) {
int doubles, i, ints, lines;
char newline;
FILE *out;
int x, y, z;
newline = '\n';
if (argc != 5) {
printf("Usage is x y z output_filename\n");
return 0;
}
if (checkInt(argv[1]) != 0)
return 0;
ints = atoi(argv[1]);
if (checkInt(argv[2]) != 0)
return 0;
doubles = atoi(argv[2]);
if (checkInt(argv[3]) != 0)
return 0;
lines = atoi(argv[3]);
out = fopen(argv[4], "a");
if (out == NULL) {
perror("File could not be opened");
return 0;
}
for (x = 0; x < ints; x++) {
int n = ReadInteger();
printf("%d\n", n);
fprintf(out, "%d\n", n);
}
for (y = 0; y < doubles; y++) {
double d = ReadDouble();
printf("%lf\n", d);
fprintf(out, "%lf\n", d);
}
for (z = 0; z < lines; z++) {
char *l = ReadLine();
printf("%s\n", l);
fprintf(out, "%s\n", l);
free(l);
}
fclose(out);
return 0;
}
int checkInt(char *arg) {
int x;
x = 0;
while (arg[x] != '\0') {
if (arg[x] > '9' || arg[x] < '0') {
printf("Improper input. x, y, and z must be ints.\n");
return -1;
}
x++;
}
return 0;
}
myio.c
#include <limits.h>
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
char *ReadInput(int fd) {
char buf[BUFSIZ];
int i;
char *input;
int r, ret, x;
i = 1;
r = 0;
ret = 1;
input = calloc(BUFSIZ, sizeof(char));
while (ret > 0) {
ret = read(fd, &buf, BUFSIZ);
for (x = 0; x < BUFSIZ; x++) {
if (buf[x] == '\n' || buf[x] == EOF) {
ret = -1;
break;
}
input[x*i] = buf[x];
r++;
}
i++;
if (ret != -1)
input = realloc(input, BUFSIZ*i);
}
if (r == 0)
return NULL;
input[r] = '\0';
input = realloc(input, r+1);
return(input);
}
int ReadInteger() {
char *input;
int go, num, x;
go = 0;
do {
go = 0;
printf("Input an integer\n");
input = ReadInput(STDIN_FILENO);
for (x = 0; x < INT_MAX; x++) {
if (x == 0&& input[x] == '-')
continue;
if (input[x] == 0)
break;
else if (input[x]> '9' || input[x] < '0') {
go = 1;
printf("Improper input\n");
break;
}
}
} while (go == 1);
num = atoi(input);
free(input);
return num;
}
double ReadDouble(void) {
int dec, exp;
char *input;
int go;
double num;
int x;
do {
go = 0;
dec = 0;
exp = 0;
printf("Input a double\n");
input = ReadInput(STDIN_FILENO);
for (x = 0; x < INT_MAX; x++) {
if (x == 0&& input[x] == '-')
continue;
if (input[x] == 0)
break;
else if (input[x] == '.' && dec == 0)
dec = 1;
else if (x != 0&& (input[x] == 'e' || input[x] == 'E') && exp == 0) {
dec = 1;
exp = 1;
}
else if (input[x]> '9' || input[x] < '0') {
go = 1;
printf("Improper input\n");
break;
}
}
} while (go == 1);
num = strtod(input, NULL);
free(input);
return num;
}
char *ReadLine(void) {
printf("Input a line\n");
return(ReadInput(STDIN_FILENO));
}
char *ReadLineFile(FILE *infile) {
int fd;
fd = fileno(infile);
return(ReadInput(fd));
}
myio.h
#ifndef _myio_h
#define _myio_h
/*
* Function: ReadInteger
* Usage: i = ReadInteger();
* ------------------------
* ReadInteger reads a line of text from standard input and scans
* it as an integer. The integer value is returned. If an
* integer cannot be scanned or if more characters follow the
* number, the user is given a chance to retry.
*/
int ReadInteger(void);
/*
* Function: ReadDouble
* Usage: x = ReadDouble();
* ---------------------
* ReadDouble reads a line of text from standard input and scans
* it as a double. If the number cannot be scanned or if extra
* characters follow after the number ends, the user is given
* a chance to reenter the value.
*/
double ReadDouble(void);
/*
* Function: ReadLine
* Usage: s = ReadLine();
* ---------------------
* ReadLine reads a line of text from standard input and returns
* the line as a string. The newline character that terminates
* the input is not stored as part of the string.
*/
char *ReadLine(void);
/*
* Function: ReadLine
* Usage: s = ReadLine(infile);
* ----------------------------
* ReadLineFile reads a line of text from the input file and
* returns the line as a string. The newline character
* that terminates the input is not stored as part of the
* string. The ReadLine function returns NULL if infile
* is at the end-of-file position. Actually, above ReadLine();
* can simply be implemented as return(ReadLineFile(stdin)); */
char *ReadLineFile(FILE *infile);
Related Questions
I keep getting an index out of range error on this lab



Answers
The Python code for parsing food data is given. This code first reads the name of the text file from the user. Then, it opens the text file and reads each line.
How to depict the codePython
import io
import sys
def parse_food_data(file_name):
"""Parses food data from a text file.
Args:
file_name: The name of the text file containing the food data.
Returns:
A list of dictionaries, where each dictionary contains the following information about a food item:
* name: The name of the food item.
* category: The category of the food item.
* description: A description of the food item.
* availability: Whether the food item is available.
"""
with io.open(file_name, 'r', encoding='utf-8') as f:
food_data = []
for line in f:
data = line.strip().split('\t')
food_data.append({
'name': data[0],
'category': data[1],
'description': data[2],
'availability': data[3] == '1',
})
return food_data
if __name__ == '__main__':
file_name = sys.argv[1]
food_data = parse_food_data(file_name)
for food in food_data:
print('{name} ({category}) -- {description}'.format(**food))
This code first reads the name of the text file from the user. Then, it opens the text file and reads each line. For each line, it splits the line into a list of strings, using the tab character as the delimiter. It then creates a dictionary for each food item, and adds the following information to the dictionary:
Learn more about code on
https://brainly.com/question/26497128
#SPJ1
Can someone help me with this? Heres the question.
Use the function written in the last lesson to calculate the gold medalists’ average award money for all of their gold medals. Define another function in your program to calculate the average.
Your program should then output the average award money, including the decimal place. Your program should use a total of two functions. You may assume that the user will provide valid inputs.
Sample Run
Enter Gold Medals Won: 3
How many dollars were you sponsored in total?: 20000
Your prize money is: 245000
Your average award money per gold medal was 81666.6666667
Answers
The written programme that determines the average reward sum for a specified number of gold medals and total prize money is provided below.
What does the code above refer to?The entire award money is determined by dividing the total reward money by the number of gold medals using the first function, calculate award money. Therefore, The average prize money is determined by dividing the total prize money by the number of gold medals using the second function, calculate average.
Return calculate award money(gold medals, total prize money) / gold medals in the function def calculate average(gold medals, total prize money).
medals gold = int
"Enter Gold Medals Won: " input
ttal prize money = int("How much money were you sponsored overall? ");
Gold medals and the total reward money are used to compute the award money.
calculate average(gold medals, total prize money) = average award money
print(award money, "Your prize money is:")
print("Your average gold medal award was," average award money) ("Your average gold medal award was," average award money)
To know more about programme visit:-
https://brainly.com/question/30307771
#SPJ1
In 25 words or fewer, explain how u can help maintain a productive work environment while on the job
Answers
I would ensure side attractions like gisting or surfing the internet while I am supposed to be working are eliminated while also personalizing my space.
Internet Retailing
Visit an e-commerce Web site such as Amazon.com and find a product you would like to purchase. While looking at the page for that item, count the number of other products that are being offered on that page.
Activity
Answer the following questions: What do they have in common? Why are they appearing on that page?
Answers
When I visited the e-commerce Web site such as Amazon.com and find a product that I would like to purchase which is a laptop, The thing that the sellers have in common is that they are trusted and verified sellers, their product presentation is nice and has warranty on it. The reason they are appearing on that page is because the product are similar.
What is E-commerce site website?The term e-commerce website is one that enables customers to buy and sell tangible products, services, and digital commodities over the internet as opposed to at a physical store. A company can process orders, receive payments, handle shipping and logistics, and offer customer care through an e-commerce website.
Note that there are numerous eCommerce platforms available, each with its own set of characteristics. The optimal eCommerce platform will therefore rely on your demands, available resources, and business objectives.
So, for instance, if you're a novice or small business owner looking to set up an online store in only a few clicks, go with a website builder like Hostinger. Oberlo, on the other hand, boasts the best inventory management system for dropshippers and is the top eCommerce platform overall.
Learn more about e-commerce Web site from
https://brainly.com/question/23369154
#SPJ1
factor that affects the evolution of technology
Answers
Answer:
perceived attributes of change, social influence, facilitating conditions and individual characteristics.
Assume a 2^20 byte memory:
a) What are the lowest and highest addresses if memory is byte-addressable?
b) What are the lowest and highest addresses if memory is word-addressable, assuming a 16-bit word?
c) What are the lowest and highest addresses if memory is word-addressable, assuming a 32-bit word?
Answers
a) Lowest address: 0, Highest address: (2^20) - 1. b) Lowest address: 0, Highest address: ((2^20) / 2) - 1. c) Lowest address: 0, Highest address: ((2^20) / 4) - 1.
a) If memory is byte-addressable, the lowest address would be 0 and the highest address would be (2^20) - 1.
This is because each byte in the memory requires a unique address, and since there are 2^20 bytes in total, the highest address would be one less than the total number of bytes.
b) If memory is word-addressable with a 16-bit word, each word would consist of 2 bytes.
Therefore, the lowest address would be 0 (representing the first word), and the highest address would be ((2^20) / 2) - 1.
This is because the total number of words is equal to the total number of bytes divided by 2.
Subtracting 1 gives us the highest address, as the addresses are zero-based.
c) If memory is word-addressable with a 32-bit word, each word would consist of 4 bytes.
In this case, the lowest address would still be 0 (representing the first word), and the highest address would be ((2^20) / 4) - 1.
Similar to the previous case, the total number of words is equal to the total number of bytes divided by 4.
Subtracting 1 gives us the highest address.
For more questions on address
https://brainly.com/question/30273425
#SPJ8
The Boolean operators include which of the following?
A. and, or, not
B. to, for, from
C. a, an, the
D. is, are, not
Answers
Answer:
The answer is A. and, or, not
Explanation:
Using a Boolean search can help narrow your results. A Boolean search is a query that uses the Boolean operators AND, OR, and NOT, along with quotation marks, to limit the number of results. For example, searching the terms Alexander the Great AND conquests will provide results about Alexander, great, and their conquests.
What is the value of X when line 30 is executed in the program below:
10 X = 5
20 X = X + 5
30 X = X/5 + X
40 X = X * 5
50 X = (X - 5)/5
this is for qbasic btw
any helpis appreciated pls only correct answers
Answers
Answer:
X = 12
Explanation:
The primary value of X is 5. In line 20 X = X + 5, which is saying the primary value of X ,5, + 5, this is going to return the value of X to now become 10. Now the primary value of X in the program has changed to 10.
In line 30 X = X/5 + X, keeping in mind that the new primary value is not 5 but 10. So now line 30 is saying X = 10/5 + 10. This return the value of X to be 12.
Fritz is a big fan of the racerville rockets. unfortunate;y, the team has been accused of cheating during their games. Fritz reads many articles and posts about this developing news story. His social media algorithms have "learned" that he's a fan of the team, so his feed doesnt show him any articles that argue the accusations are true. From this, Fritz decides his favorite team must be innocent of all cheating charges. Fritz is now in
A. a filter bubble
B. A third party
C. A subculture
D. an echo chamber
Answers
Option(D) is the correct answer. Fritz is now in an echo chamber.
Fritz's situation aligns with the concept of an echo chamber. An echo chamber refers to an environment, such as social media, where individuals are exposed to information and opinions that reinforce their existing beliefs and perspectives.
In this case, Fritz's social media algorithms have filtered out articles that present arguments in favor of the cheating accusations, creating an echo chamber that only confirms his preconceived notion of the team's innocence.
As a result, Fritz is insulated from diverse viewpoints and alternative perspectives, which can hinder critical thinking and a comprehensive understanding of the situation.
for similar questions on Fritz.
https://brainly.com/question/5100081
#SPJ8
( _____)once demonstrated that a rigid wing on an aircraft would break more often than a flexible wing. Will give BRAINLIEST.
Answers
Answer:
the Wright brothers
Explanation:
Wing warping was an early system for lateral (roll) control of a fixed-wing aircraft. The technique, used and patented by the Wright brothers, consisted of a system of pulleys and cables to twist the trailing edges of the wings in opposite directions.
Answer:
the Wright Brothers
Explanation:
I know
Count operation Lucky twos
Lucky Twos determines and displays the number of digits that are 2s in a whole number. For example, the number of 2s in 3487 is 0, while the number of 2s in 272521 is 3. Note: whole numbers are non-negative integers starting at zero 0, 1, 2, 3, 4.
Assume that the fractional part is discarded in the division:
10 / 4 = 2
8 / 5 = 1
20 / 3 = 6
Read number
set count to 0
while number > 0
If the number module 10 is Then add
1 to count
End If
Compute number as number / 10
End while
Display count.
Let n be the number of digits of the whole number. What is the number of operations that are executed in the code in terms of n?
Answers
Answer:
Following are the solution to this question:
Explanation:
Its complexity of both the pseudo-code described is indeed proportional to the number of digits. So, how often number there are in this specific number is the query. Whenever a number is considered, the d digit would be between \(10^{(d-1)}.\) inclusive exclusive \(10^d\) That would be as, let d become the number of digits at N, and the inequalities, They can tell
\(10^{(d-1)} \leq N < 10^d\)
We get, we take a logarithm,
\(d-1 \leq \log(N) < d\)
The increase of 1 to the left inequality, \(d \leq \log(N)+1\), and Combining the previous outcome, we got, \(\log(N) < d \leq \log(N) + 1\). That's would be to say, that number of number d by \(O(\log(N))\) is higher and lower. Consequently, the number of transactions in the code is \(O(\log(N))\)
We have that the number of operations that are executed in the code in terms of n is mathematically given as
The quantity of operations done in the code is O(log(N))
Operation
Generally the equation for the is mathematically given as
If we think about a number,
with d digits is between 10^(d-1) inclusive and 10^d exclusive.
Let d be the wide variety of digits in N
10^(d-1) <= N < 10^d
d-1 <= log(N) < d
d <= log(N) + 1,
The Inequality
log(N) < d <= log(N) + 1.
Therefore
The quantity of operations done in the code is O(log(N))
For more information on Inequality visit
https://brainly.com/question/19491153
give the full form of GUI
Answers
Explanation:
graphical user interface
Answer:-
GUI ➺ Graphical User Interface.
How To Approach Data Center And Server Room Installation?
Answers
Answer:
SEE BELOW AND GIVE ME BRAINLEST
Explanation:
Make a plan for your space: Determine how much space you will require and how it will be used. Consider power requirements, cooling requirements, and potential growth.
Choose your equipment: Based on your unique requirements, select the appropriate servers, storage devices, switches, routers, and other equipment.
Create your layout: Determine the room layout, including rack placement, cabling, and power distribution.
Set up your equipment: Install the servers, storage devices, switches, and other equipment as planned.
Connect your equipment: Connect and configure your servers and other network devices.
Check your systems: Check your equipment to ensure that everything is operating properly.
Maintain and monitor: To ensure maximum performance, always check your systems for problems and perform routine maintenance.
Ethics in Al can contribute toward social progress and boost positive changes in society. Which aspect should be removed to achieve this change society ?
A. safety
B. management
C. bias
D. law
Answers
Answer: Hayaa~!
The answer is: . c. bias
Is known when someone purposefully biased an answer towards what they belive or think, this can be avoided by not asking them about topics that we firmly believe they are biased.
Explanation: I took the test
Hope this Helps
-Aaden<3
Jackson is visiting his cousin over summer vacation. While visiting, he decides to check his email. Jackson notices that the computer he is working on is incredibly slow and is connected to the network through a series of telephone lines. He is also unable to use the home telephone while he is connected to the internet. Which of the following types of network connection is Jackson using?
A.
digital subscriber line
B.
cable broadband line
C.
fiber optics line
D.
dial-up internet line
Answers
Note that in this case, Jackon is using a "dial-up internet line" (Option D)
What is a dial-up internet line?Dial-up Internet access is a type of Internet access that uses the public switched telephone network's infrastructure to connect to an Internet service provider by calling a phone number on a traditional phone line.
Dial-up The Internet has been available since the 1980s through public providers such as NSFNET-connected institutions. In 1989, the BBC offered Internet connection through Brunel University in the United Kingdom. Pipex in the United Kingdom and Sprint in the United States were the first to commercially provide dial-up in 1992.
Learn more about dial-up internet line:
https://brainly.com/question/3521554
#SPJ1
Data Privacy may not be applicable in which of the following scenarios?
Answers
Answer:
A platform being hosted in a country with no DP laws but targeted at data subjects from a country with stringent laws.
Explanation:
No Data Privacy laws mean that there is a high likelihood of data being leaked to various third parties and unwanted websites.
Countries with stringent laws like China have a government that wants full control over the data of their people and the transaction of data from each of them in order to better monitor them.
website is a collection of (a)audio files(b) image files (c) video files (d)HTML files
Answers
Website is a collection of (b) image files (c) video files and (d)HTML files
What is websiteMany websites feature a variety of pictures to improve aesthetic appeal and provide visual substance. The formats available for these image files may include JPEG, PNG, GIF, or SVG.
To enhance user engagement, websites can also introduce video content in their files. Web pages have the capability to display video files either by embedding them or by providing links, thereby enabling viewers to watch videos without leaving the site. Various formats such as MP4, AVI and WebM can be utilized for video files.
Learn more about website from
https://brainly.com/question/28431103
#SPJ1
Which term means a session level protocol that is fast and efficient but has no means forever control or acknowledgment
Answers
Answer: User Datagram Protocol (UDP)
Explanation:
User Datagram Protocol (UDP) is a term that means a session level protocol that is fast and efficient but has no means for error control or acknowledgment.
The User Datagram Protocol is also referred to as a communications protocol which helps in the exchange of messages in network.
investigation on how to feed pets technology sub
Answers
The field of pet feeding technology has seen significant advancements in recent years, with a range of new products and solutions being developed to help pet owners feed their pets more effectively and efficiently.
One popular technology in pet feeding is the automatic pet feeder. These feeders use timers and sensors to dispense food at predetermined times, allowing pet owners to set a feeding schedule and ensure that their pets are getting the right amount of food, even when they are not at home. Some automatic feeders also have features such as portion control and the ability to dispense different types of food, making them a convenient and versatile solution for pet owners.
Another type of pet feeding technology is the connected pet feeder. These feeders use Wi-Fi or other wireless technologies to connect to a smartphone or other device, allowing pet owners to remotely control the feeding schedule, monitor food levels, and receive alerts when the feeder needs to be refilled. Some connected feeders also have features such as video cameras, which allow pet owners to watch their pets eat from anywhere.
There are also smart pet feeders that use artificial intelligence and machine learning to tailor feeding schedules to the individual needs of each pet. These feeders can track a pet's eating habits, learn their preferred meal times and portion sizes, and adjust the feeding schedule accordingly. This type of technology can help pet owners ensure that their pets are getting the right amount of food and can also help prevent overeating and related health issues.
In addition to these products, there are also various apps and services available that help pet owners manage their pet's feeding. For example, there are meal planning apps that help pet owners track their pet's food intake and make sure they are getting the right nutrients. There are also services that provide custom-made pet food, formulated to meet the specific nutritional needs of each individual pet.
In conclusion, there are a variety of technologies available for pet owners to help them feed their pets more effectively and efficiently. From automatic feeders and connected feeders to smart feeders and meal planning apps, these technologies offer a range of solutions that can help pet owners ensure that their pets are getting the right amount of food and the right nutrients.
What is one way a lender can collect on a debt when the borrower defaults?
Answers
Answer:
When a borrower defaults on a debt, the lender may have several options for collecting on the debt. One way a lender can collect on a debt when the borrower defaults is by suing the borrower in court. If the lender is successful in court, they may be able to obtain a judgment against the borrower, which allows them to garnish the borrower's wages or seize their assets in order to pay off the debt.
Another way a lender can collect on a debt when the borrower defaults is by using a debt collection agency. Debt collection agencies are companies that specialize in recovering unpaid debts on behalf of lenders or creditors. Debt collection agencies may use a variety of tactics to try to collect on a debt, including contacting the borrower by phone, mail, or email, or even suing the borrower in court.
Finally, a lender may also be able to collect on a debt when the borrower defaults by repossessing any collateral that was pledged as security for the debt. For example, if the borrower defaulted on a car loan, the lender may be able to repossess the car and sell it in order to recover the unpaid balance on the loan.
Explanation:
How many outcomes are possible in this control structure?
forever
if
is A button pressed then
set background image to
else
set background image to
Answers
Answer:
In the given control structure, there are two possible outcomes:
1) If the condition "Is A button pressed?" evaluates to true, then the background image will be set to a specific value.
2) If the condition "Is A button pressed?" evaluates to false, then the background image will be set to another value.
Therefore, there are two possible outcomes in this control structure.
Hope this helps!
can somebody help what's wrong with this code
asap~

Answers
Answer:
There's a + missing to concatenate your variable to your string.
Is this statement true or false? To change the color of text, you must select the entire text to be changed.
Answers
Answer:
true is the correct answer to your questions
Use the drop-down menu to identify the strategy for programming a solution.
When you have a problem that seems too large to manage, it might be smart to try
solution.
Even if you do not know the programming language being used, you could still use
to communicate specific programming ideas to your colleagues.

Answers
A. When you have a problem that seems too large to manage, it might be smart to try an incremental solution.
B. Even if you do not know the programming language being used, you could still use pseudocode to communicate specific programming ideas to your colleagues.
What is the problem?If you face a kind of hard challenge, it may be better to be clever to attempt a strategy of breaking it down into smaller, and also a more manageable tasks. This approach requires dividing the issue into smaller and more feasible segments and then addressing each segment separately.
So, Pseudocode serves as a simplified format of coding, utilized for explaining an algorithm in simple terms. One can utilize it for delineating the procedural sequence of a program without being excepted in the particulars of a particular coding language.
Learn more about programming language from
https://brainly.com/question/16936315
#SPJ1
What is resource Management in Wireless Communication ? Explain its Advantages?
Answers
Answer:
Resource management is the system level transmission cellular networks and wireless communication.
Explanation:
Wireless communication is the process to continue to the address for faster response time,to the resource management.
Transmission is the provided by that more utilization and wireless resources available,and to discovered data.
Wireless communication system to demand the larger bandwidth and transmission using development to the system.
Wireless communication resources management the larger bandwidth and reliable transmission consumed all the system layer.
Resource management techniques tool are used in a preliminary concepts or mathematical tools,and average limited power battery.
Resource management are they necessary mathematical and fundamental tools are used in wireless communication.
Wireless communication in the provide that wireless industry in a wireless communication.
true or false. Two of the main differences between storage and memory is that storage is usually very expensive, but very fast to access.
Answers
Answer:
False. in fact, the two main differences would have to be that memory is violate, meaning that data is lost when the power is turned off and also memory is faster to access than storage.
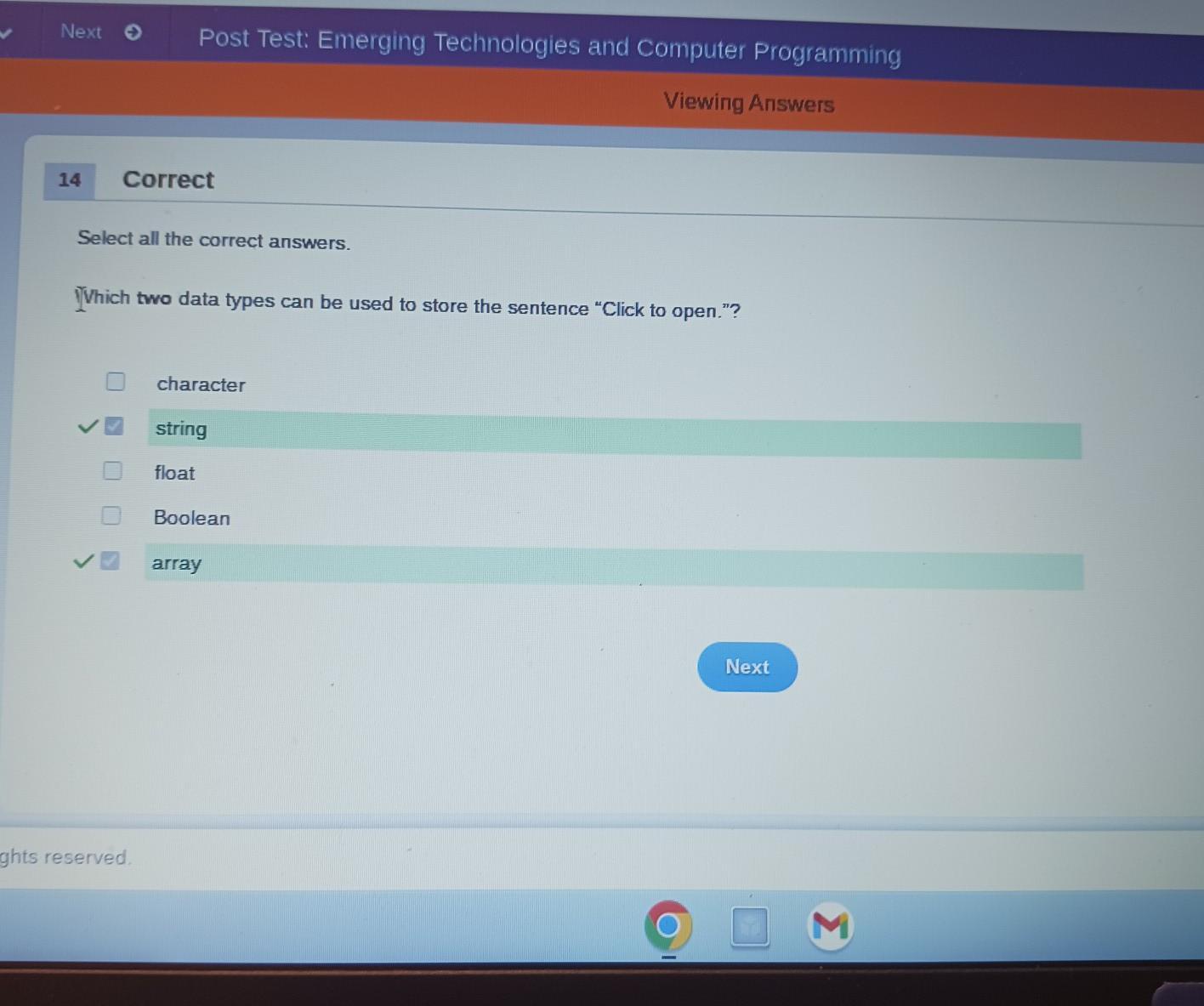
PLEASE HELP there are TWO ANSWERS
Select all the correct answers.
Which two data types can be used to store the sentence "Click to open."?
character
string
float
Boolean
array
Answers
Answer:
boolean is correct
Explanation:
Answer:
its string and array
Explanation:
Edmonton gang
Photographs that are too dark or too light can be difficult to fix with photo-editing software.
True
False
Answers
where was this taken

Answers
Answer:
Mostar city
Explanation:
look at the architecture
Answer:
rome:)
Explanation:
Which option would allow you to watch an HD video, without delays in playback, on a computer with a Mac OS and a connection that has a lower bit rate? MPG QuickTime H.264 Flash Player
Answers
Answer:
H.264
Explanation:
A file type can be defined as the standard used to store digital data such as pictures, texts, videos, and audios. They all have unique file extension which determines the type of software program (application) to be used for opening a particular file and accessing its data e.g pictures (jpeg, png), texts (txt, docx, rtf), audios (mp3, acc), and videos (mp4, 3gp, avi, h.264, mkv).
Sometimes, computer users make the mistake of opening files with the wrong software application or program, this often leads to an error due to the incompatibility of the software application with the particular file.
H.265 is a high efficiency video codec (HEVC) and it's a standard video compression codec designed and developed to offer a better data compression, as an upgrade to the advanced video coding (AVC) standard.
Hence, the option or file extension (format) which would allow you to watch a high definition (HD) video, without delays in playback, on a computer with a Mac operating system (OS) and a connection that has a lower bit rate is the H.264 format.